Remote debugging is a feature of the ICEbearPlus extended debugging toolchain. It enables you to grant access to a locally running debug agent by using SSH tunneling feature of the third party application Putty. For example, if your hardware shows a problem in the field or development of a new flash driver is required, debugging service can be provided by us without the requirement to send hardware. So the steps for a service technician are:
- (Inform sysadmin about the action to avoid paranoia)
- Obtain Putty.exe from putty.org
- Run it
- Configure the tunnel
- Start the debug agent
Configuring the tunnel session
Add the host name and port as shown below. You may want to get back to this menu later and Save this session for later use.
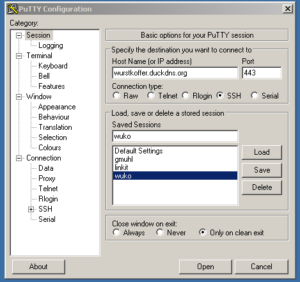
When you make a connection, a black terminal window pops up and will ask you for login data (sent to you separately).
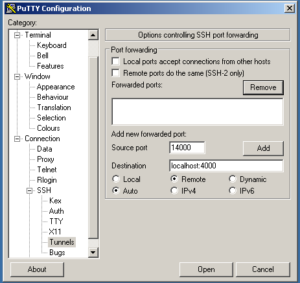
Configure the tunnel
To grant access to a local port of your computer, the tunnel needs to be configured as ‘Remote’, i.e. the ‘Source port’ of the remote host is forwarded to the local port. Means, an authorized person logged in on the remote server can connect to your local port as long as Putty is active.
To open a remote port forward, add ‘Source port’ and ‘Destination’ as shown below and click ‘Add’. Do the same for both ports 2000 and 4000 for the local gdbproxy server, such that the settings are displayed in the image on the bottom.
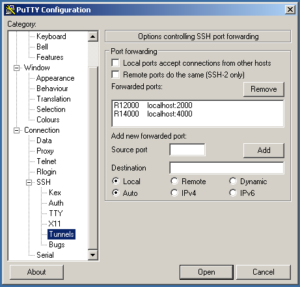
Then you can connect using ‘Open’.
gdbproxy debugging
Start the gdbproxy server via the Start menu through the ICEbear->Start gdbproxy entry.
Then the gdbserver should fire up as shown below.
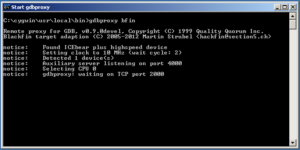
Once a connection is made, you can see this on the console. Also, the status during debugging is displayed. If the connection through the tunnel is effective (i.e. Putty tunnel session active) a connection can be made.
A safety notice: No other person aware of this information can connect to your target. Only authorized persons with a login can access your local ports during an active session. Once you terminate the Putty session by closing the window, all connections are terminated and no more access from outside is possible.
Service package
Available remote debugging services:
- Analog Devices Blackfin targets (ICEbearPlus and service contract required)
- netpp node or dombert IP camera hardware (ZPUng)
- ARM based systems supported by OpenOCD

